
Identity Orchestration
Intelligent access that replaces cost, risk, and complexity with speed, security, and scale.

Great for IT and great for users
Digital transformation is accelerating, and IT is on point to help scale and respond to rapidly changing business requirements. With IT resources at a premium, identity orchestration simplifies authentication, authorization, and risk policy decisions for all user types. This translates to increased security, reduced complexity, and a better user experience.
Provision users and apps
Orchestrate and automate the provisioning and deprovisioning of users and applications using protocols like SCIM and REST APIs. Provision and deprovision IDaaS users within various applications and services using automation to ensure a seamless and secure onboarding and offboarding experience for all your users. Provision users into IDaaS from Azure AD to create a single source of truth and ensure only active and authorized users with the right roles are enabled within IDaaS.

Benefits
Simplify identity management
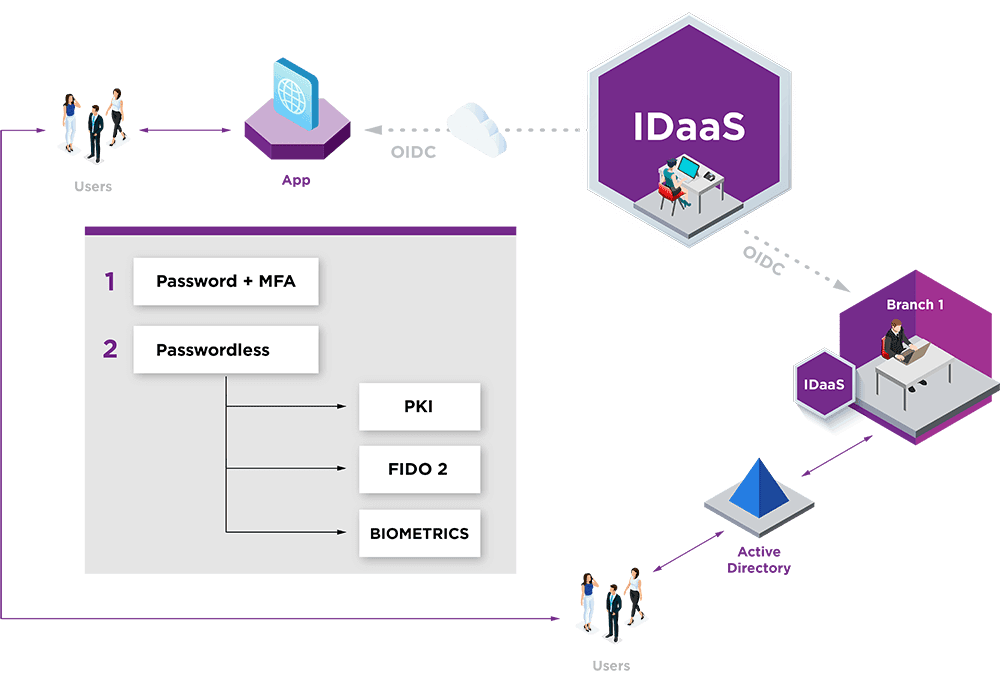
Eliminate manual user provisioning across multiple disconnected systems with support for modern authentication protocols including SAML, OIDC, OAuth, and SCIM. As well, user self-service tools provide for a better IT and user experience.
Stop user churn and grow revenues
Realize frictionless UX with self-service onboarding, seamless login including passwordless options, and adaptive risk-based authentication.
Eliminate identity silos
Unify disparate IAM systems with centralized identity management that removes the complexity of authentication. The result is increased security and a better experience for users and IT alike.
Prevent data breaches and fraud
Be contextual with real-time analytics and our risk-based policy engine. Apply step-up authentication when conditions warrant for a secure and frictionless user experience.
Scale with your user base
Change the way your organization manages identities. Remove complexity and inefficiencies while also improving the security and experience of your growing user community.
An Entrust Identity portfolio specialist will be in touch with options soon.
Identity Portfolio
Our identity portfolio capabilities:
Authenticate
Streamline the onboarding of diverse users and devices with a wide range of technologies.
Authorize
Ensure both strong security and exceptional user experiences with these best-in-class technologies.
Transact and Manage
Continuously protect against advanced threats with technology from behavior analytics to fraud detection.
The identity portfolio suited to your authentication needs
Consumer
Consumer Banking
Attract and retain customers with best-in-class mobile and online banking services.
Customer Portals
Give customers frictionless access to your portals — and build a great brand experience.
CIAM Integration
Our portfolio integrates seamlessly with your customer identity and access management (CIAM) strategies.
Meet PSD2 Regulations
We have the trusted identity tools you need to help you be successful and in compliance.
Workforce
Physical/Logical Access
Our portfolio offers the necessary technologies to integrate physical and logical secure access.
Privileged Worker
Protect the critical application credentials of system administrators or senior leaders.
Passwordless Login
Get a passwordless SSO solution that supports all devices, PCs and Macs, and cloud and on-premises apps.
Enable PIV Compliant Government Mobility
Remove complexity and enable highly secure mobility with proven PIV solutions.
Citizen
Digital Citizen
Use our portfolio to secure and manage passports, national IDs, and driver's licenses.
