
Identity Fraud Detection
When it comes to transaction security, you need to defend customer data, enterprise data and your brand reputation. We offer proven approaches to prevent your enterprise from making the wrong kind of headlines.
Fight consumer fraud with Entrust Identity
Global identity fraud losses topped $56 billion in 2020 with financial institutions, businesses, and consumers all feeling the pain. Mitigating the risk of fraud not only helps contain these costs but is also essential to building and maintaining consumer trust.
Mitigate fraud risk
Our authentication solutions are built to help you automatically detect and prevent fraud. Through adaptive technologies, our platform grows smarter and more capable over time – which helps defend against increasingly sophisticated attacks.
Benefits
Reduce Fraud Risk
Device reputation checks, digital identity proofing, behavioral biometrics, and user behavior analytics proactively detect fraudulent patterns for quick remediation.
Prevent Fraud
Automatically stop active threats, such as malware and phishing, with pre-determined responses including user notification, step-up authentication, session termination, and account lockout.
Curtail Fraud Costs
Minimize false alerts, fraudulent claims, and actual fraud losses with early detection and automated resolutions.
Protect Consumers
Continuously and invisibly verify consumer identities with adaptive risk-based authentication. Stop would-be cybercrooks from taking over accounts and/or creating fraudulent new ones.
Secure Mobile Apps
Employ runtime application self-protection (RASP) security to protect the integrity of mobile apps with real-time threat monitoring.
Secure Transactions
One-click transaction signing with verification and non-repudiation for secure digital payments. Safeguard ecommerce sales with 3DS compliance for card-not-present (CNP) transactions.
Protect Your Brand and Reputation
Build and maintain consumer trust by proactively keeping consumer identities, data, and transactions secure.
Related Entrust Identity as a Service Resources
An Entrust Identity portfolio specialist will be in touch with options soon.
Identity Portfolio
Our identity portfolio capabilities:
Authenticate
Streamline the onboarding of diverse users and devices with a wide range of technologies.
Authorize
Ensure both strong security and exceptional user experiences with these best-in-class technologies.
Transact and Manage
Continuously protect against advanced threats with technology from behavior analytics to fraud detection.
The identity portfolio suited to your authentication needs
Consumer
Consumer Banking
Attract and retain customers with best-in-class mobile and online banking services.
Customer Portals
Give customers frictionless access to your portals — and build a great brand experience.
CIAM Integration
Our portfolio integrates seamlessly with your customer identity and access management (CIAM) strategies.
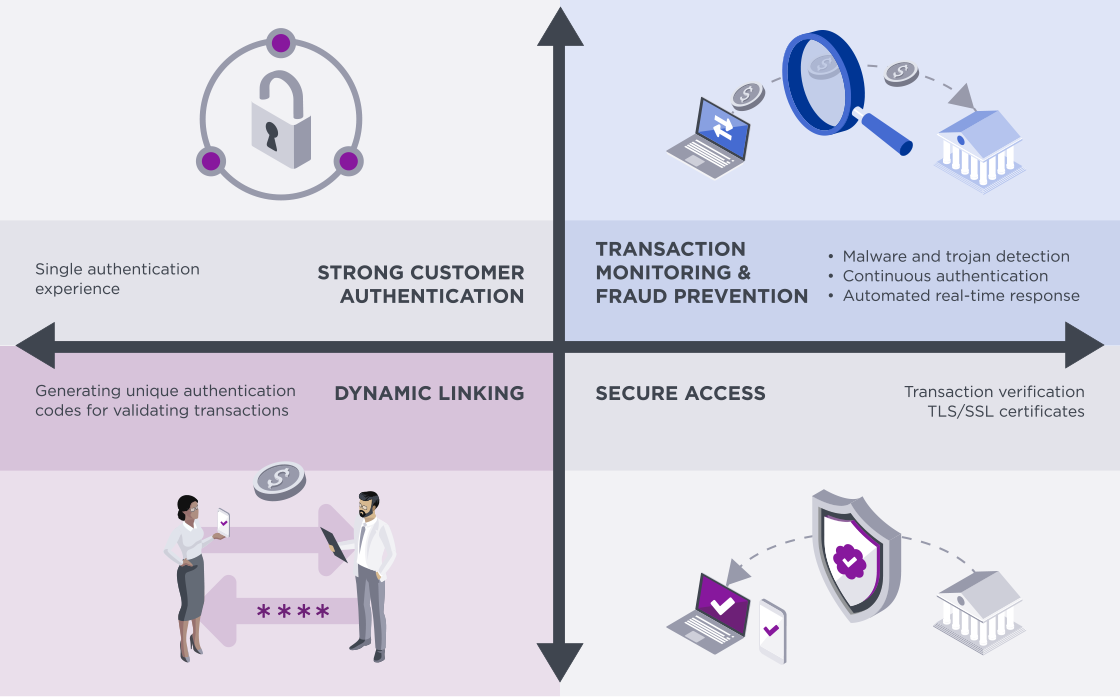
Meet PSD2 Regulations
We have the trusted identity tools you need to help you be successful and in compliance.
Workforce
Physical/Logical Access
Our portfolio offers the necessary technologies to integrate physical and logical secure access.
Privileged Worker
Protect the critical application credentials of system administrators or senior leaders.
Passwordless Login
Get a passwordless SSO solution that supports all devices, PCs and Macs, and cloud and on-premises apps.
Enable PIV Compliant Government Mobility
Remove complexity and enable highly secure mobility with proven PIV solutions.
Citizen
Digital Citizen
Use our portfolio to secure and manage passports, national IDs, and driver's licenses.
Get Entrust Identity as a Service Free for 60 Days
Explore the Identity as a Service platform that give you access to best-in-class MFA, SSO, adaptive risk-based authentication, and much more.
