Build Trust at Every Touchpoint
Verify identities, issue trusted credentials, navigate KYC compliance, and fight fraud across digital and physical channels with Entrust. We help financial institutions deliver multi-layered security, advanced fraud detection, secure payment card issuance, and seamless digital experiences across banking, lending, payments, fintechs, and more.
Saved in fraud losses for our global client base in the last year alone.
Source: Identity Fraud Report 2025.
Of U.S. financial institutions say cybersecurity breaches are their most immediate fraud concern.
3-year ROI for some Entrust customers through discounted costs, staff productivity enhancements, and improved business results.
Build Trusted Financial Journeys
Deliver secure, frictionless experiences across the user lifecycle.
From onboarding and identity verification to secure physical and digital card issuance and high-risk transaction authentication, Entrust helps protect every financial moment with AI-driven fraud detection and support for global KYC and AML compliance.
Solutions Made for Modern Finance
Identity Verification
Leverage a library of global IDV signals – including AI-powered document and biometric technology – to build trust with minimal friction while still securing your business from fraud and helping to address compliance needs at scale.
Financial Card Issuance
Issue secure debit, credit, and prepaid cards – on-site or centrally – with advanced personalization and activation tools to boost engagement.
Digital Signing
Sign anywhere in the world with the security and reliability you need. Operate quickly, efficiently, and digitally with Advanced Electronic Signatures, Qualified Electronic Signatures, and document sealing.
Hardware Security Modules
Protect cryptographic assets and digital transactions with FIPS-certified HSMs – on-prem or as-a-service – for banking-grade security and compliance.
Phishing-Resistant Access
Prevent fraud and reduce account takeover risk with adaptive, risk-based authentication using biometrics, phishing-resistant passkeys and certificates, plus seamless step-up verification for strong security with low-friction access.
Compliance Management
Accelerate your path to KYC, AML, PSD2, and eIDAS compliance with out-of-the-box workflows and ongoing policy enforcement.
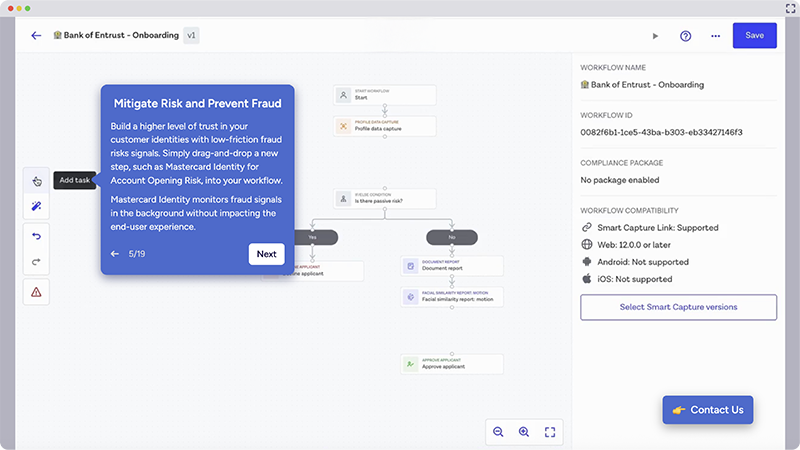
Acquire New Users, Prevent Fraud, and Simplify Compliance
Seamless Onboarding
Speed up identity checks and reduce drop-off rates using AI-powered biometric, document, and data verification that builds trust from the first moment of interaction for financial services security.
AI-Powered Fraud Prevention
Reduce fraud losses and prevent risk. Detect deepfakes, forgeries, and synthetic identities across high-risk moments with AI that’s trained in real-world situations.
Enhanced User Experience
Deliver secure digital-first experiences based on how your users want to engage: mobile, web, mail, or in-branch.
Scalable, Flexible Orchestration
Drive operational efficiency at scale. Launch and iterate fast with low/no-code tools, SDKs, and configurable workflows tailored to unique risk profiles and use cases.
Simplified KYC and AML Compliance
Help meet local and global KYC and AML requirements, and scale into new markets with ease, with built-in support for ETSI, NIST, and other regional standards.
Full Lifecycle Coverage
Get a unified view of user identities, securing users from onboarding and account creation to transactions and continuous monitoring with integrated issuance and authentication.
Solutions for Every Financial Need
Identity Verification
Verify real customers during onboarding with document, biometric, and data-driven checks that help reduce fraud and friction while supporting KYC and AML requirements at scale.

Card & ID Issuance
Issue trusted physical and digital payment cards securely and efficiently – supporting central issuance and mail fulfillment, plus activation and engagement across digital and branch experiences.

Authentication
Protect accounts and transactions with risk-based authentication, passkeys, and step-up methods that help reduce account takeover while keeping the user experience smooth.

Key & Certificate Lifecycle Management
Manage keys, certificates, and secrets across their full lifecycle with centralized visibility and automation – helping reduce operational risk, prevent outages, and support compliance.

Post-Quantum Cryptography
Plan and transition to quantum-safe cryptography with crypto-agility and post-quantum readiness to protect long-lived financial data and digital trust as threats evolve.

Risk-Based Authentication (RBA)
Assess risk in real time across onboarding and transactions using adaptive signals and analytics to help prevent fraud, reduce false positives, and support smoother customer experiences.

Related Resources
U.S. Financial Trends Survey
Explore key fraud, cybersecurity, and identity trends shaping U.S. financial institutions.
Consumer Payment Preferences in APAC
Download this report to discover consumer banking survey insights.
Payment Preferences in Africa
Learn about Sub-Saharan Africa banking customers’ payment preferences and expectations.
Global Banking & Finance Awards 2025
See why Entrust was recognized for innovation and leadership in financial security and digital trust.
Gartner® Magic Quadrant™ for Access Management
See why Gartner named Entrust a Challenger for a third consecutive year in the 2025 Magic Quadrant for Access Management.
Gartner® Magic Quadrant™ for Identity Verification
Learn why Gartner named Entrust a Visionary in the 2025 Magic Quadrant for Identity Verification.
2026 Identity Fraud Report
Discover the latest insights on identity fraud and how to prevent it.
Hear experts from the American Bankers Association and Entrust discuss how banks can use digital identity technology to their advantage.
The Business Value of Entrust
IDC surveyed six Entrust customers to quantify the value and benefits of using Entrust data security solutions.
Build Digital Trust with Biometric Authentication
56% of consumers state that they would switch banks after a fraud incident - yet 68% say they'd use biometric authentication if it means better protection. See more financial survey results.
Contact one of our solution specialists for a demo or to discuss your financial security use cases and needs.