Bring Your Own Key, Hold Your Own Key, Double Key Encryption
Strengthen the security of your sensitive data – in any cloud environment
With nShield® Bring Your Own Key and Cloud Integration Option Pack, you bring your own keys to your cloud applications, whether you’re using Amazon Web Services (AWS), Google Cloud Platform (GCP), Microsoft Azure or Salesforce. Entrust nShield high-assurance HSMs let you continue to benefit from the flexibility and economy of cloud services while you strengthen the security of your key management practices and gain greater control over your keys.
Benefits
Safer Key Management
Backed by FIPS 140-2 Level 2 and 3 nShield HSMs, Entrust nShield BYOK helps you adopt safer key management practices that strengthen the security of your sensitive data in the cloud.
Stronger Control Over Your Keys
With Entrust nShield Bring your Own Key, you use your own Entrust nShield HSMs in your own environment to create, store and securely export your keys to the cloud.
Superior Key Generation
Entrust nShield HSMs use a certified, high-entropy random number generator to create keys of higher quality than typically generated in software.
Specifications
Certified Hardware Root of Trust Entrust
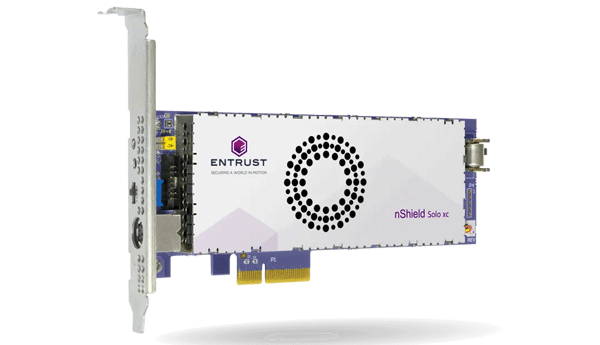
nShield BYOK is based on nShield Edge, Solo and Connect HSMs, which are certified to FIPS 140-2 Level 2 and 3. This certification ensures that Entrust nShield HSMs have been tested to stringent standards, including for their tamper-resistance features. See our product pages for complete lists of standards these platforms comply with.
Entrust nShield BYOK for Microsoft Azure
You can bring your own keys (BYOK) to your cloud applications. For Microsoft Azure, use the nShield Cloud Integration Option Pack to generate your keys on premises, and then securely transfer your keys to the Entrust nShield HSM running within the Azure infrastructure. With this approach, you get HSM-backed security at both ends. You can also store and manage your master keys in your on-premises Entrust nShield HSM.
nShield BYOK for AWS and GCP
If you’re using AWS or GCP, you will use the nShield Cloud Integration Option Pack to generate your keys on-premises and lease them to AWS or GCP for temporary use in the cloud. After a pre-determined time period, your keys in the cloud will be destroyed. If needed, you can again lease the keys stored in your HSM.
nShield BYOK for Salesforce
Using nShield Cloud Integration Option Pack allows you to import keys generated on an nShield HSM into Salesforce.
Multi-cloud Service
Entrust nShield BYOK lets you choose your cloud service provider, even from the same HSM. Your on-premises Entrust nShield HSM will send keys to whichever cloud provider you choose, whenever you choose.