In the first blog post within our Cybersecurity Awareness Month series, we talked about the various types of attacks against multi-factor authentication (MFA).
As we’ve learned, not all MFA authenticators are built the same. Some offer higher assurance levels and better protection than others. Choosing the right MFA configuration will depend on the type of resources protected and the users accessing these resources. Let’s take a look at some common MFA authenticators and the types of attacks they are vulnerable to below.
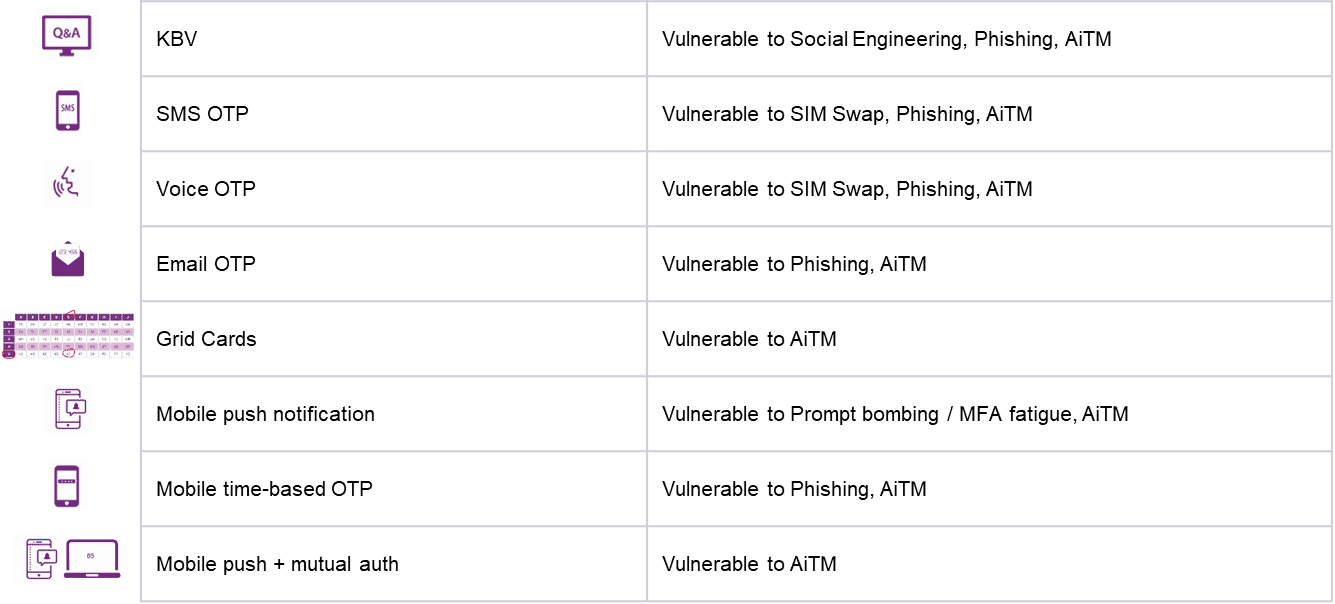
Knowledge-Based Verification (KBV) – Knowledge-Based Verification methods include your security Q&As. These are the weakest form of authentication after passwords as they typically contain questions like your dog’s name, sibling or parents’ names, favorite car, etc., all of which can be obtained through social engineering or through publicly available data on social media sites that you are a part of. In addition, this method is also vulnerable to the common MFA attacks such as phishing and Adversary in the Middle (AiTM).
One-Time Password (SMS OTP, Voice OTP, Email OTP) – While authenticators like SMS OTP, voice OTP, and email OTP may be convenient from a user experience and adoption perspective, they do not offer a high level of assurance and are vulnerable to various types of cyberattacks. SMS OTP and voice OTP are susceptible to the SIM swap, phishing, and AiTM attacks, while email OTP is susceptible to phishing and AiTM attacks.
Mobile Push Notification – This is a more secure authentication method as it involves the use of biometrics in the form of face ID or touch ID to unlock your mobile device to allow a push authentication. Yet it is still vulnerable to prompt bombing or MFA fatigue attacks as seen in recently in the news.
Mobile Time-Based OTP – These are your soft token authenticators that generate new codes every 30 seconds or so. They are more secure since they include biometrics to unlock, but they are still vulnerable to phishing and AiTM attacks.
Mobile Push + Mutual Authentication – This method combines mobile push notifications with mutual authentication tokens to provide additional protection. In this method, the user may also be shown a mutual authentication token on the website or app they are trying to authenticate into. They must confirm on their mobile authenticator app, which adds an addition layer of protection, but is still vulnerable to a sophisticated AiTM attack.
The above authenticators, while adding higher security than the basic password, may satisfy some use cases or levels of assurance. However, for higher security and assurance, organizations must consider authentication that involves the use of PKI-based smart credentials or FIDO2 tokens.
FIDO2 Key – FIDO2 keys are physical keys like USBs that a user plugs into the desktop. In some of them, there is also a place for scanning your fingerprint as a second factor of authentication. The key contains encrypted information, which is used to authenticate user identity when plugged in. Once used successfully, the user is automatically logged into the system and gains access to all relevant applications in a single session.
Credential-Based Passwordless Access – Credential-based passwordless access provisions a digital certificate onto the user’s phone (mobile smart credential), transforming it into their trusted identity. Due to Bluetooth®/NFC capabilities, as the user walks toward a workstation, a connection is established between the mobile device (where the smart credential resides) and the desktop. There can be two options to passwordlessly log in from here – either the system gets unlocked when the user is asked to provide their fingerprint or face ID on the smartphone, or the desktop prompts the user to enter a PIN to log in. In the same session, the user can also connect securely with a remote desktop and SSH.
FIDO2 Passkeys – This is a newer passwordless authentication method that is gaining importance and adoption due to the improved user experience and security. In this method, when a user tries to authenticate into an application or service, the application issues a security challenge to the registered smart device in proximity (confirmed via Bluetooth). The user then uses biometrics to authenticate the passkey on the mobile device, which is then used to sign and send back the challenge. The Bluetooth requires physical proximity, which means that there is now a phishing-resistant way to leverage the user’s smartphone during authentication. With this capability, the user’s phone will be able to upgrade to a higher security level (phishing resistance) without the need for the user to carry a specialized piece of authentication hardware (security keys).
It’s important to note that any of the above passwordless solutions can be combined with single sign on for an additional layer of security, where the user can seamlessly access applications using federated identity protocols like SAML/OIDC.
Learn more about adaptive MFA that the Entrust identity and access management platform offers here and contact us to learn how we can help you implement and rollout a secure adaptive MFA solution with high assurance passwordless capabilities for your users.



