For those of you old enough to remember Second Life, among the many ‘firsts’ that made it notable was a virtual currency that had direct real-world value. If you made and sold items in Second Life, you could trade Linden Dollars for actual currency.
These days, cryptocurrencies and non-fungible tokens (NFTs) are hot investments – representing new forms of digital assets that are disrupting traditional financial services. With large financial infrastructure players such as CME, ICE and Fidelity now trading cryptocurrency, a growing list of traditional banks including JP Morgan, Standard Charter, and Nomura are already taking cryptocurrency customers, and even companies such as MicroStrategy are acquiring Bitcoin as a ‘capital allocation strategy’. It’s clear we are witnessing a rapid expansion of the digital asset market and the exponential growth of the role of digital asset custodians.
Established financial services providers have had many years to define how the traditional products and solutions are sold and operated, but digital assets custodians are still in their infancy. As a result, these are largely unregulated, leaving many options with differing approaches and strategies relating to keeping the assets safe. Some forward thinking custodian platforms are already adopting security approaches that are mandated by the likes of GDPR, eIDAS and FIPS to ensure their customers have appropriate protection and their financial stability is safeguarded.
The biggest attack threats for digitals assets are the misuse of private keys. These threats can be broken down to three categories:
- External threats – Hackers, malware, trojans horse attacks
- Internal threats – Disgruntled staff, human error, fraud, duty of care
- A blend of both! – Social engineering, bribery, corruption, coercion
The question is how to keep the keys associated with your digital assets and/or wallet safe?
Just as you wouldn’t leave the keys to your house under the mat, Hardware Security Modules (HSMs) help ensure encryption or signing keys are securely stored and never made available for people to copy or steal.
Compared to software solutions, HSMs provide a protected environment, isolated from the application host, for key generation and data processing. Did you know that a simple program can search the virtual memory or disks in a server to find cryptographic key material? See if you can pick out which of the 5 blocks in the memory visualization below is the cryptographic key.
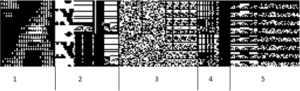
The answer is section 3 – which stands out due to its random, white noise-type pattern. That’s what a key looks like – as opposed to a more structured appearance that application data (represented in block 1, 2, 4, 5) tends to have.
HSMs ensure cryptographic keys are secured when not in use, reducing the attack surface, and providing control over who is granted access to the keys and what they can do with them.
This is where Entrust comes into the picture. Entrust nShield HSMs are FIPS 140-2 Level 3 certified, high-performing, and easy-to-integrate. They facilitate regulatory compliance and deliver the highest levels of data and application security for enterprise, financial and government organizations. The unique nShield Security World key management architecture provides strong, granular controls over access and usage of keys across on-premise and multi-cloud environments.
We also now offer nShield-as-a-Service – a subscription based solution offering the same features and function as the physical hardware but are attractive to digital asset custodians, many of them start-ups, who don’t operate their own data centers. There’s also the benefit of no upfront cost and a predictable monthly charge.
In a world rife with both internal and external security challenges, HSMs protect your cryptographic keys, assuring digital asset custodians against unauthorized access to data and identity.
You can find out more about how you can keep the keys to your digital kingdom safe and sound here: https://www.entrust.com/digital-security/hsm



