What is an Encrypted Email? Meaning & How it Works
An encrypted email is a method in which the sender of the email can ensure that only the recipient will be able to read the content of the message. The goal of the encrypted email is to protect sensitive data whether it’s because an unauthorized user gains access to the email communications channel or if an internal user accidentally emails it to the wrong recipient.
Should Emails be Encrypted?
The biggest risk to an organization not securing their emails is that it leaves them vulnerable to email hacking activities, which can result in theft of their intellectual and capital property as well as damage to their brand and erosion of customer trust. There are also certain compliance risks that organizations can face depending on their sector or jurisdiction in which they do business. Business email compromise (BEC) attacks have been exploding in recent years, moving across geographies and business sectors. According to the most recent FBI Internet Crime Reports (ICRs), organizations in the U.S. lost $8.6 billion to BEC attacks from 2014 to 2021 – with $2.4 billion of that in 2021 alone.
What Dangers Can Organizations Experience from Email Attacks?
There are two types of email hacking activities:
- Phishing: When generic messages are delivered to a wider pool of potential victims
- Spear phishing or business email compromise (BEC) attacks: Specific and planned targeted attacks to an individual or a group; these attacks aim to:
- Extract sensitive information
- Install malware onto the network
- Wire money to accounts that belong to the attackers
What are the Benefits of Email Encryption?
Signing and encrypting emails helps organizations to prevent email hacking that results in theft of intellectual and capital property. It also mitigates brand and reputational damage that can occur if an enterprise loses control over sensitive data. In addition adopting digitally signed and encrypted email technology addresses the associated fall out that can cause various companies to fail various compliance regulations such as HIPAA and GDPR. Meeting and maintaining compliance with various privacy and security regulations reduces the risk of businesses paying high penalties for non-compliance.
Which Regulations Require Encrypting Emails?
Depending on the sector, geography or where the enterprise operates in, Organizations need to pay attention to different regulations. For example, in the U.S., the Health Insurance Portability and Accountability Act (HIPAA) requires that organizations protect sensitive patient health information from being disclosed without a patient’s knowledge or consent. According to the U.S. Department of Health and Human Services, HIPAA violation costs in 2020 alone were $13 million.
In the European Union, the General Data Protection Regulation (GDPR) guidelines state that personal data must be fully protected, and if it’s not, organizations can be subjected to fines of up to 4% of their preceding year’s revenue or up to 20 million euros. In Denmark for example, as an extension to GDPR encrypting emails containing sensitive personal information has been obligatory for businesses since 2019.
Why is Email a Threat within the Healthcare Industry?
Phishing attacks are still a leading cause of data breaches in healthcare and according to the FBI’s internet crime report organizations lost $2.4B to BEC attacks. A phishing attack is often the first step in a multi-stage attack that sees malware or ransomware subsequently deployed.
After Phishing attacks, the HIPAA Journal - Healthcare Data Breach Report suggests that email-related breaches in healthcare are the second most common type of attack.
In 2021 the Office for Civil Rights (OCR) investigated 277 healthcare email breach incidents 83% of which were a result of hacking or IT incidents.
Email account breaches were reported at a rate of more than 1 every two days in 2020, but email-related breaches took second spot this year behind breaches of network servers. Network servers often store large amounts of patient data and are a prime target for hackers and ransomware gangs.
How Does Email Encryption Work?
There are currently two approaches to secure email:
- PGP (Pretty Good Privacy)
- S/MIME (based on RSA and x.509 certificates)
OpenPGP and S/MIME are very similar in some respects: they both provide authentication via digital signatures and privacy via data encryption. Although OpenPGP has many supporters, it has considerably less support in the marketplace. S/MIME is more widely supported by software vendors, and it is incorporated into most common email clients.
With public key encryption, there are two keys: One can be made public, and the other is kept private. The sender encrypts messages using the recipient’s public key. The recipient decrypts the message using his private key. If a message is being sent to multiple recipients, the email is encrypted separately by every recipient's public key.
Digital signatures use the same public/private key pairs, but in reverse. The sender takes a secure hash of the message and encrypts that hash using his/her own private key. Anyone can decrypt that hash (and verify it by running the same hash against the original message) simply by decrypting with the sender’s public key. Since only the owner of the private key associated with that public key could possibly have encrypted it, the message can be verified. This provides integrity and non-repudiation. Non-repudiation because the sender can't later deny they did not send the message.
Entrust S/MIME solution provides organizations with a capability to dramatically reduce the risk of company data loss originating from email. Entrust’s identity and end-to end encryption capabilities supported for internal and external emails, together with the deployment automation and lifecycle management capabilities, enable organizations to improve their compliance and security posture relative to other solutions.
Does SSL Work on Email?
RSA is the only public key cryptographic protocol supported for signing and encrypting Email. SSL/ TLS certificates cannot be used for that purpose. However, there are other encryption technologies that work together with S/MIME to provide protection for messages in-transit. For example: Transport Layer Security (TLS) or previously Secure Sockets Layer (SSL). These protocol encrypt the tunnel or the route between email server, to help prevent snooping and eavesdropping. They also encrypt the connection between email client and email server. S/MIME can work with them but is not dependent on them.
Does VPN Encrypt Email?
VPN does not encrypt email. It is not a tool to prevent hacking, viruses or malware and it doesn't help safeguard contents within the email nor help authenticate the email sender.
What Does Encrypting an Email Do?
The act of digitally signing and encrypting an email enables an employee to prove that the attachments and content originated from the sender’s email address and that it hasn’t been modified during the transit. This is also known as non-repudiation and can be backed up in a court of law through various legislation.
Providing employees within an enterprise with access to their own S/MIME certificates, can make it easier to identify the recipient and identity of the sender, which in turn can help limit the impact of a Business Email Compromised (BEC) attack.
Entrust S/MIME certificates include the names of the organization, individual, and email address enabling email recipients to distinguish SPAM or Phishing emails from the emails of a legitimate sender.
What Does Signed and Encrypted Email Look Like in Outlook and Apple Mail?
It is very easy to distinguish what a trusted email experience looks like with Secure Email Certificate setup in Microsoft Outlook and MacOS. Below you can see visuals of four different instances:
- signed email
- encrypted email
- signed and encrypted email
- unsigned and unencrypted email
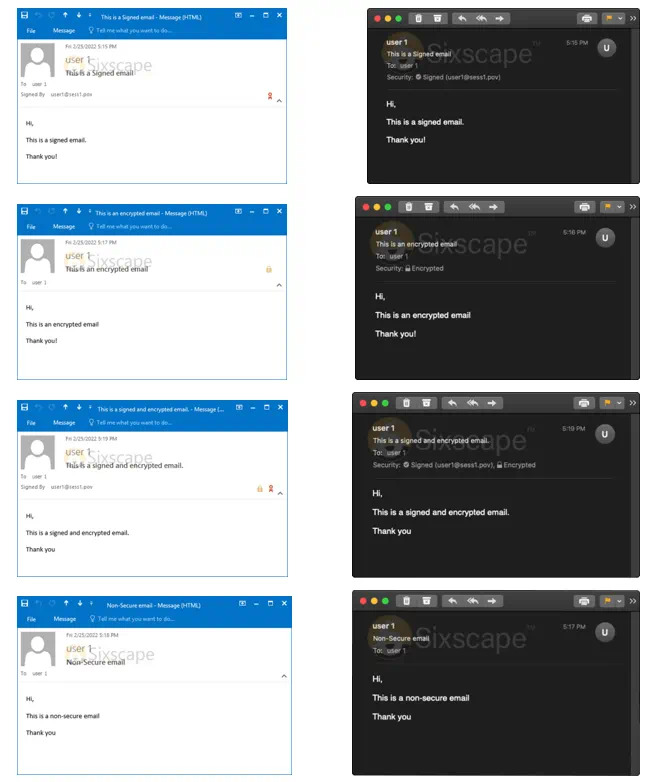
There are three primary trust indicators in the Outlook and MacOS experience:
- the red ribbon, which shows that this email is signed.
- the padlock icon, which shows that the email is encrypted.
- you can verify the identity of the sender on the left of the email that it was signed by user 1 an employee of X company.
By contrast, in the untrusted email experience an unsigned and unencrypted email does not display nor a ribbon or a padlock. In this case it is technically possible for the from address user 1 to be spoofed.
Please note, these features are available once both users have interchanged their public keys.
How to Sign and Encrypt Email on Your Mobile Device?
When there is an S/MIME certificate installed on the device Android or an iPhone device, on the right of the screen, you can see it displays an open and a closed padlock. In order to send an encrypted email all the user has to do is tap on the padlock icon.
Emails can be signed automatically if you activate this option in settings.

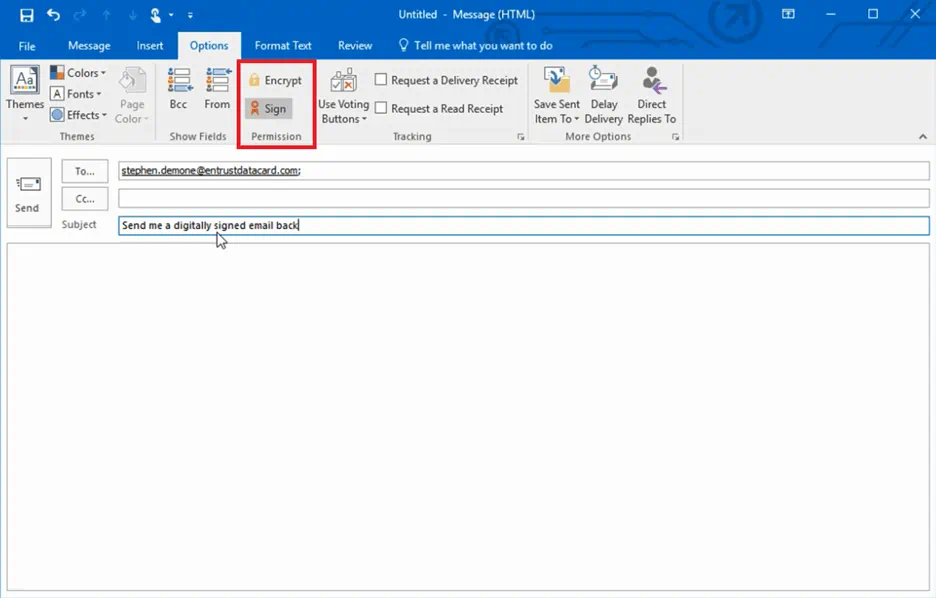
How to Encrypt and Sign an Email with an S/MIME Certificate?
To Sign or/and Encrypt an Email Message, you should simply click the Sign or/and Encrypt buttons that appear on a Compose Message email dialogue under the Options tab.
Explore Sections
- Should Emails be Encrypted?
- What Dangers Can Organizations Experience from Email Attacks?
- What are the Benefits of Email Encryption?
- Which Regulations Require Encrypting Emails?
- Why is Email a Threat within the Healthcare Industry?
- How Does Email Encryption Work?
- Does SSL Work on Email?
- Does VPN Encrypt Email?
- What Does Encrypting an Email Do?
- What Does Signed and Encrypted Email Look Like in Outlook and Apple Mail?
- How to Sign and Encrypt Email on Your Mobile Device?
- How to Encrypt and Sign an Email with an S/MIME Certificate?



