Is there a mandate within your organization to adopt the cloud and migrate some, or all, of your enterprise’s application workloads to those new environments?
Are you overwhelmed with the options available to you and even more concerned about the development effort necessary to modify your applications to adopt new technologies and to operate in a new environment?
Furthermore, for those applications requiring access to security infrastructure and key management systems, is the impact of migrating existing keys and making them available in the cloud causing your risk management and compliance teams real headaches? Especially concerning the prospect of losing control over where your keys are stored or backed up, and ensuring it is unambiguously defined as to who has access to them?
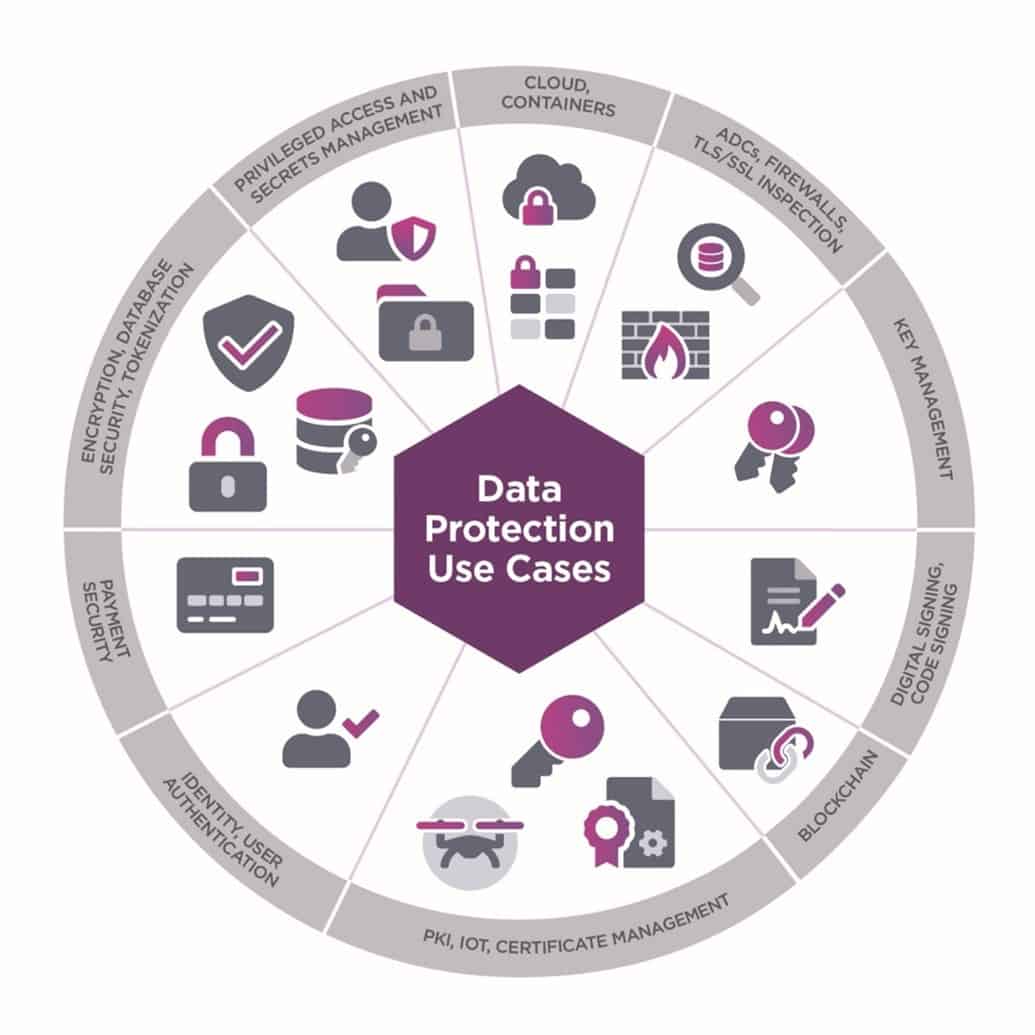
Figure 1: Illustration of the range of use cases where keys can be protected by nSaaS
Or, alternatively would you prefer to look for options offering a more considered transition and allowing you to build capacity in the cloud more slowly and/or manage your risk exposure by adopting a multi-cloud or hybrid approach to your cloud migration strategy – but are concerned about resource constraints in your security team and need a straightforward and flexible solution that will not stretch them even further than they already are?
Well, if any or all of those resonate with you, Entrust can help.
With Entrust nShield as a Service (often referred to as nSaaS) you can gain all the benefits of adopting a hosted HSM service – reduce your reliance on internal resources to feed and water the devices, manage the systems to secure their day-to-day operation, and build and maintain the infrastructure to deliver business continuity and support disaster recovery – while enabling you to seamlessly transition your application workloads without the need to make any changes and most importantly (in many cases) ensuring there is no requirement for key migration or regeneration activities.
Moreover, by leveraging the unique benefits of the nShield Security World architecture – provided as part of nShield as a Service – you can build a consistent, coherent, and ubiquitous key management solution that stretches seamlessly across your choice of multiple disparate environments, independent of which cloud service provider or on-prem/private cloud service you adopt. With Security World you can create a truly multi-cloud solution while retaining control of your cryptographic assets within the organization (regardless of workload location), managing your keys centrally and holistically through a single pane of glass. Furthermore, you retain physical assets – such as authorization tokens (smart cards) – within the enterprise to ensure only you can authorize operations.
Thus, with nSaaS you’ll never need to worry about future changes of preferred environment or the repatriation of resources or workloads back on-prem – nor be vulnerable to rogue access to orphaned instances – as your keys will always be securely available to each and every environment, enabling immediate, on-demand, frictionless, and load-balanced transactions load across your active deployments.
By deploying nSaaS and building out Security World, you retain full control of your key management solution, ensuring all keys are generated and protected by secrets within the secure confines of HSMs dedicated to your use – with nobody sharing resources critical to retaining security – and with access to those keys controlled by identity and access management systems in the enterprise domain and key access control defined by you.
So, if you’re concerned about how you will securely transition to the cloud, mitigate compliance risks, and satisfy your auditor’s requirements for key management controls while minimizing the impact to your application environment, why not talk to Entrust about evaluating nSaaS?
nSaaS is a globally available service with availability zones spread around the world, hosting Entrust’s market-leading FIPS 140-2 Level 3 certified nShield Connect HSMs and available on a flexible subscription-based approach that delivers the performance and scale you require. And with the nSaaS geo-location coverage, and its adjacency to the cloud provider’s infrastructure, latency to your deployment environment is reduced, minimizing the impact of using disparate environments while enabling you to comply with data sovereignty requirements or local regulations on data residency.
Furthermore, nSaaS supports all major application programming interfaces (APIs), making the connection to your new workload environment identical to your on-premises setup, ensuring that no application changes are required to adopt the service.
Why not join the wide range of enterprises who want to embrace the scale and flexibility offered by the cloud, reducing their own data center footprint and saving on internal resources, but wanting to retain maximum control of their cryptographic services.



