MMC (Cybersecurity Maturity Model Certification)
Libro electrónico: Prepárese para la CMMC
¿Qué es CMMC? ¿Qué debe hacer su organización para prepararse? ¿Y qué soluciones de Entrust pueden ayudarlo a preparar la CMMC? Lea este libro electrónico para averiguarlo.

Entrust facilita el cumplimiento de la CMMC para que las redes de contratación sigan apoyando al Departamento de Defensa y otras agencias gubernamentales.
La Certificación del Modelo de Madurez de Ciberseguridad (CMMC) es un programa establecido por los EE. UU. El Departamento de Defensa (DoD), para asegurar y proteger la Información de Contratos Federales (FCI) y la Información no Clasificada Controlada (CUI), exige la certificación de los contratistas externos en 14 dominios diferentes, cada uno con tres niveles específicos de certificación.
CMMC es un estándar de ciberseguridad para la red de contratistas del Departamento de Defensa. La cadena de suministro de dicha red incluye a más de 300000 empresas. CMMC es la respuesta del Departamento de Defensa para proteger información confidencial en los sistemas de los contratistas.
- La CMMC se lanzó el 1 de enero de 2020.
- Desde el 30 de noviembre de 2020, el Departamento de Defensa incorpora requisitos CMMC en determinadas RFP/RFI.
- Para el 1 de octubre de 2025, todas las adjudicaciones del Departamento de Defensa requerirán al menos algún nivel de certificación CMMC. Aunque el Departamento de Defensa es el catalizador de la CMMC, ahora gana terreno en la Base Industrial de Defensa (DIB), el Departamento de Seguridad Nacional y otras agencias federales, espacialmente después de SolarWinds.
¿Está listo para cumplir la CMMC?
Históricamente, correspondía a los contratistas implementar, monitorear y certificar la seguridad de sus sistemas de tecnología de la información y cualquier información confidencial del Departamento de Defensa que esos sistemas almacenaban o transmitían.
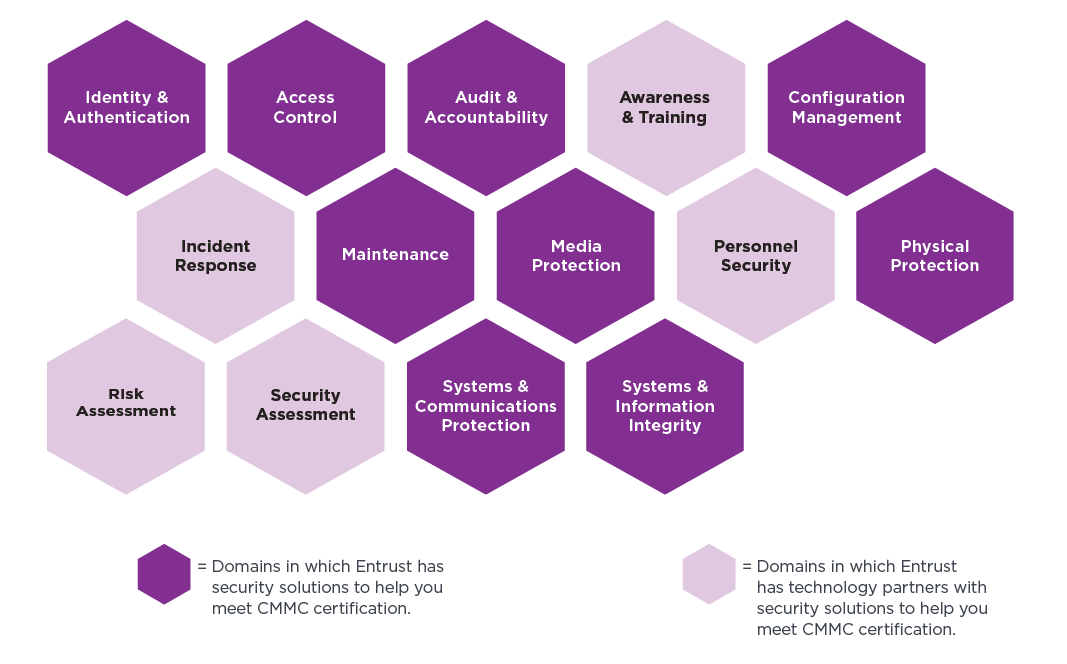
Desde el 30 de noviembre de 2020, el Departamento de Defensa (DoD) comenzó a incorporar los requisitos de la CMMC en determinadas RFP, RFI y contratos de investigación. Para el 1 de octubre de 2025, todas las adjudicaciones de contratos del DoD requerirán al menos algún nivel de certificación CMMC. El modelo consta de 3 niveles de madurez –fundacional, avanzado y experto– que dependen del tipo de información que se maneja. Cada nivel también tiene diferentes requisitos de evaluación como autoevaluaciones, evaluaciones por terceros o el gobierno. La cartera de seguridad digital de Entrust, que incluye soluciones de identidad, certificados y protección de datos, facilita el cumplimiento de 9 dominios de la CMMC en los tres niveles posibles de certificación.
Preguntas clave para determinar qué nivel de madurez necesita su organización
¿La organización maneja información básica, como información de contratos federales (FCI)? ¿O es información controlada no clasificada (CUI)? La FCI requiere una certificación de Nivel 1, pero la CUI requiere al menos un Nivel 2.
¿En qué se diferencia su actual postura de ciberseguridad y el nivel CMMC deseado? Es indispensable evaluar las diferencias para definir un plan de acción orientado a la madurez CMMC.
La CMMC abarca los requisitos de seguridad NIST SP 800-171 y otros requisitos con diferentes niveles de certificación. ¿Qué revelará la evaluación sobre su actual nivel ciberseguridad?
Tenga en cuenta el objetivo final de la CMMC: Mantener las FCI y CUI fuera del alcance de atacantes cibernéticos malintencionados.
Entrust está aquí para ayudar
Entrust proporciona soluciones para facilitar el cumplimiento de los siguientes 9 dominios CMMC:
Capacidad
- Establezca requisitos de acceso al sistema
- Controle los accesos al sistema interno
- Controle los accesos al sistema remoto
- Impida que usuarios y procesos no autorizados accedan a los datos
- Defina requisitos de auditoría
- Realice auditorías
- Identifique y proteja información de auditoría
- Revise y administre registros de auditoría
- Establezca directivas de configuración
- Gestione la configuración y las actualizaciones
- Otorgue acceso a entidades autenticadas
- Gestione el mantenimiento
- Identifique y marque medios
- Proteja y controle medios
- Desinfecte medios
- Proteja medios durante el transporte
- Limitar el acceso físico
- Defina requisitos de seguridad para sistemas y comunicaciones
- Controle comunicaciones en los límites del sistema
- Identificar y gestionar fallos del sistema de información
- Identificar contenido malicioso
- Monitorear redes y sistemas
- Proteger el correo electrónico
Dominios de capacidad CMMC