In a major shift, Google recently announced it plans to run its own certificate root program/store for the Chrome b. A root store is a list of digital certificates that is often pre-installed and regularly updated by the operating system or application on your computer, phone, television, and almost any other device that transmits data. Browsers rely on certification authorities (CAs) such as Entrust to issue digital certificates to authenticate and secure communications used for public trust. Historically, the Google Chrome web browser has relied on the root store/program of your operating system such as Android, Linux, Windows, and macOS.
To acquire and maintain a listing in a root store, a CA has to 1) comply with the strict policies and procedures defined by the root program; and 2) pass an annual third-party audit to ensure it is in compliance with external programs such as the CA/Browser forum Baseline requirements, Extended Validation (EV) guidelines, WebTrust and/or ETSI requirements.
Maintaining a root store is a time-consuming task, but not completely new for Google, an active member of the CA/Browser forum. The Common CA Certificate Database (CCADB), which is also used by other major browsers such as Mozilla and Microsoft as well as Google, are actively involved in public discussions about maintaining a root store to streamline their efforts for improving the efficacy of online security which consists of the audits, policies, procedures and practices of these CAs.
By managing and operating their own root store, Chrome can provide a more consistent experience across platforms. Plus, it makes it easier for Google to take actions against CAs that can’t ensure the trustworthiness that is expected of them. Here is an example of how Google reacted to former CA, Symantec, when they mis-issued certificates to Google domains in 2017:
ttps://groups.google.com/forum/#!msg/mozilla.dev.security.policy/fyJ3EK2YOP8/yvjS5leYCAAJ
Impact of Certificates Issued by Entrust
This move impacts all publicly trusted certificates issued by commercial CAs. The root certificates from Entrust have already been included in the new Chrome root store. Therefore, we expect that certificates issued by our CAs will continue to be trusted when Chrome is ready to start relying on the new root store.
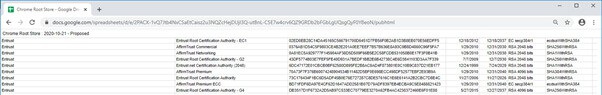
https://g.co/chrome/root-store
Impact to Private PKIs
At least for now, private CAs do not have to be installed in the Chrome browser root store. This policy differs from Mozilla Firefox where administrators must install private roots or make some configuration changes (see also: https://support.mozilla.org/en-US/kb/setting-certificate-authorities-firefox) to be included in their root store. Mozilla Firefox has been running its own root store from their inception.
Google has confirmed this with Entrust and has updated the root program website with following statement:
“No changes are currently planned for how enterprise administrators manage those CAs within Chrome. CAs that have been installed by the device owner or administrator into the operating system trust store are expected to continue to work as they do today.”
https://g.co/chrome/root-policy
To learn more about Entrust digital security solutions, visit our website.



