Certificate Signing Request (CSR) Help: CheckPoint

Certificate Signing Request (CSR) Help
CheckPoint
Before you begin...
- Never share private keys files.
- If you plan on using the same certificate on multiple servers always transfer the private key using a secure method ( e-mail is not considered a secure method of transfer ).
- It is best practice to ensure that you have current and up to date Ciphers and Protocols to ensure the best security when deploying a new Private key and Server Certificate.
- Make sure you run the SSL Server Test at the end of the installation process to check your certificate configuration against SSL/TLS Best Practices.
- For more information on SSL/TLS Best Practices, click here .
How to generate a CSR using CheckPoint appliance:
Before generating a CSR you will need to install the Root and Intermediate certificates into the Trusted CAs and Subordinate CAs.
This is a three step process:
1) Installing the Entrust Root certificate
2) Installing the Intermediate certificates
3) Creating the CSR
Part 1 of 3: Installing the Entrust Root Certificate
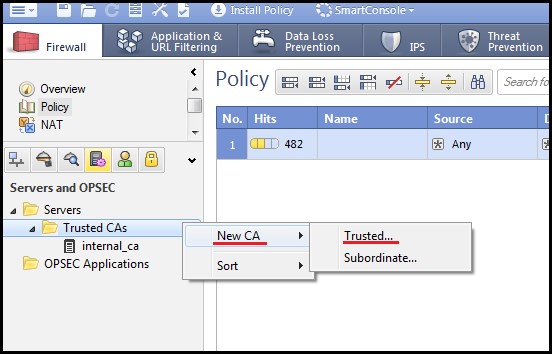
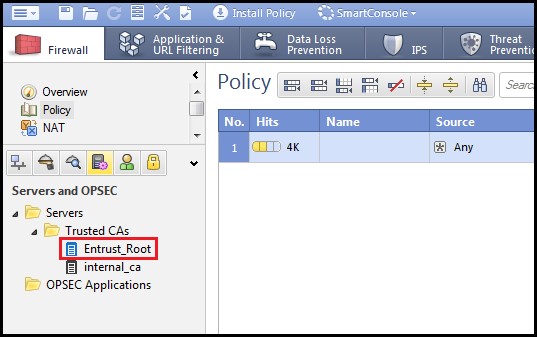
1. Open SmartDashboard and select the Servers and OPSEC tab. Right click on Trusted CAs, select New CA and click on “Trusted…”
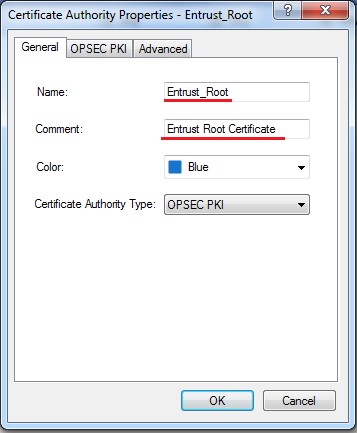
2. The Certificate Authority Properties window will appear. In the General tab, give the Root certificate a name such as “Entrust_Root”. The comment section is not mandatory but can be used to provide more information about the certificate.
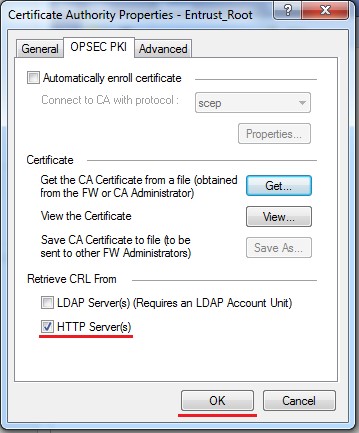
3. Select the OPSEC PKI tab and click on the “Get” button. This will allow you to select the Entrust Root certificate
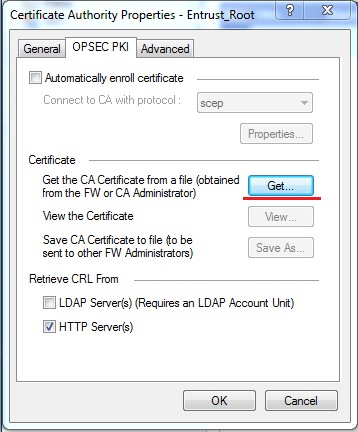
4. Locate the Entrust Root certificate commonly named Root.crt and click on Open.
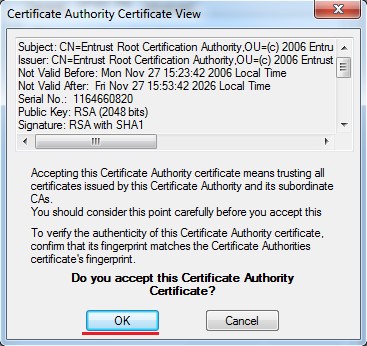
5. The Certificate Authority Certificate View window will appear. Details of the Root certificate will be displayed in the message box. Click OK to accept this certificate as a Certificate Authority.
6. You will then return to the Certificate Authority Properties window in the OPSEC PKI tab. Make sure “HTTP Server(s)” is checked and click OK.
7. The Entrust_Root CA will now be listed under Trusted CAs.
Part 2 of 3: Installing the Intermediate Certificates
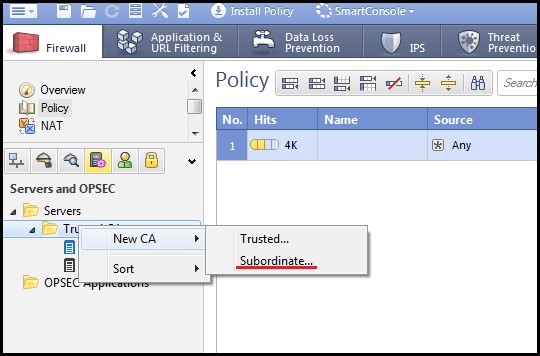
1. Open SmartDashboard and select the Servers and OPSEC tab. Right click on Trusted CAs, select New CA and click on “Subordinate...”
2. The Certificate Authority Properties window will appear. Enter a name for the Entrust Intermediate and a comment if necessary.
3. Click on the OPSEC PKI tab and click the Get button.
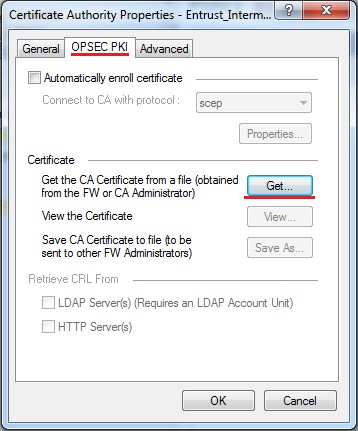
4. Next you will need to select the Entrust Intermediate file Intermediate.crt. Click Open button once you’ve selected the file.
5. The Certificate Authority Certificate View window will appear. Details of the Intermediate certificate will be displayed in the message box. Click OK to accept this certificate as a Certificate Authority Certificate.
6. The Entrust_Intermediate will now appear under Subordinate CAs.
You should now have all the required certificates installed in your SmartDashboard. The image below shows the Entrust Root and Intermediate installed.
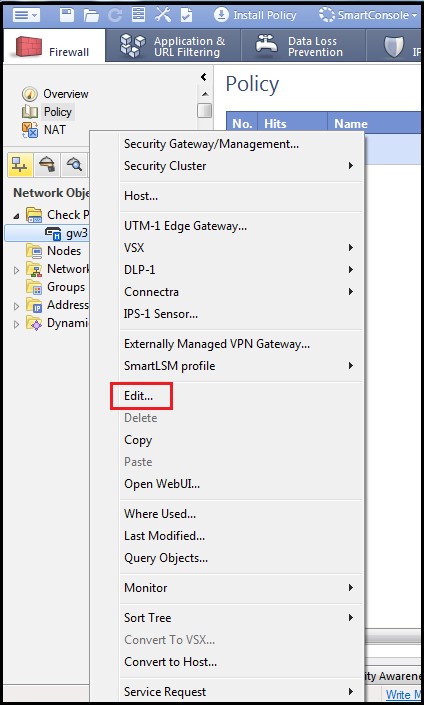
1. Double click or right click and select “Edit…” on the Network object where the certificate will be installed.
2. The Network object’s properties window appears. Click on IPSec VPN under General Properties from the left hand column and click on “Add…”
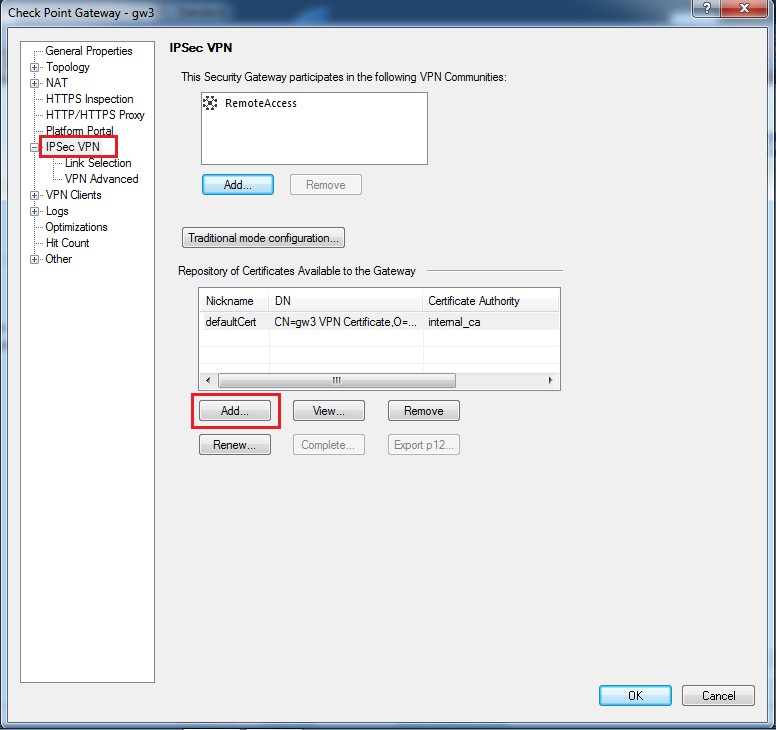
3. The Certificates Properties window will appear. Enter a nickname for the certificate such as “Entrust”. For the “CA to enroll from” field you must select the “Entrust_Intermediate”. The SSL certificate generated will be issued off the Entrust L1K, Intermediate. Click “Generate” when done.
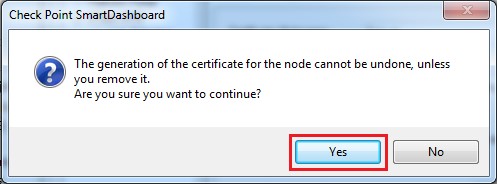
4. The informational window regarding generating a certificate for the node will appear. Click “Yes” to continue.
5. Generate Certificate Request window will appear. Enter the DN of the of the certificate in a format similar to this: CN=sslvpn.domain.com,O=Company Inc,L=City,ST=State,C=US
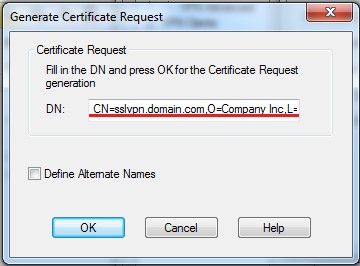
6. If you require Subject Alternate Names (SANs) in the certificate you will need to click on the “Define Alternate Names”. Click on “Add” and include the necessary SAN names. Adding SAN’s to a certificate can also be achieved in the Entrust Cloud Services Portal.
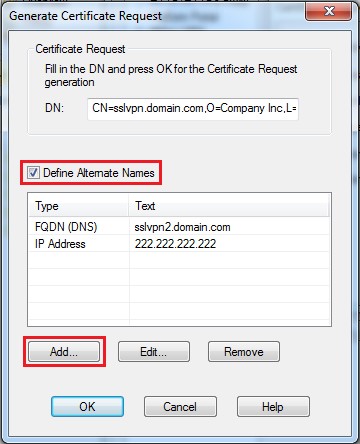
7. Click OK and the Certificate Request will be completed.
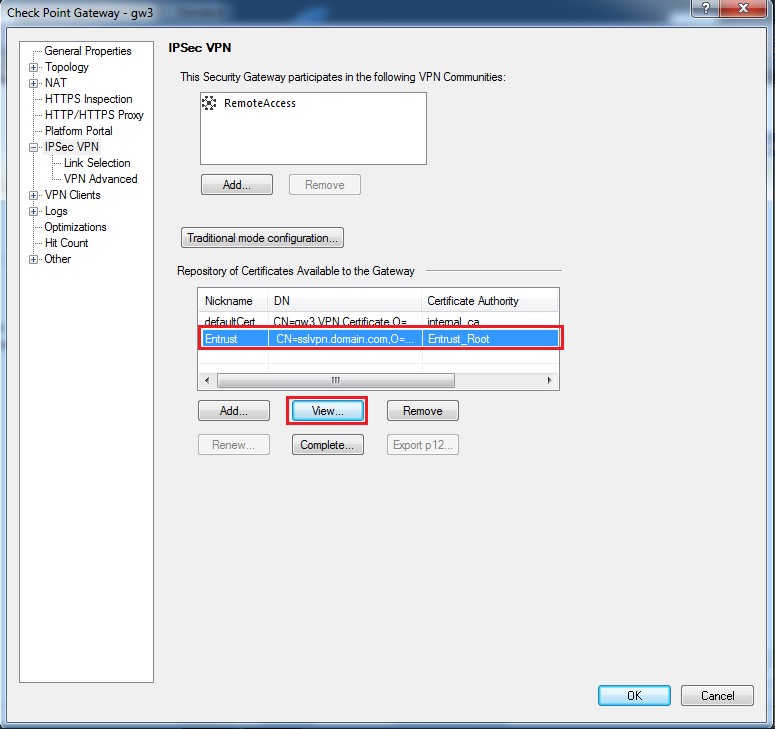
8. You will then return to the Gateway properties window. Select the Entrust certificate request you have just created in the list of Repository of Certificates Available and click “View…”
9. The Certificate Request View window will appear. You can copy the CSR by clicking on the “Copy to Clipboard” button or “Save to File…” to save the CSR to a file.
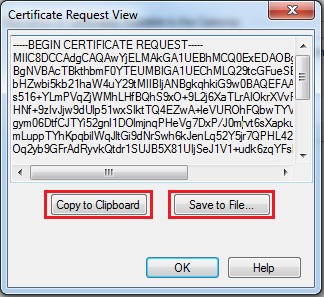
You have now completed the Certificate Signing Request on your CheckPoint appliance. Paste the CSR in the Entrust portal or the order to create the certificate.
If you have any questions or concerns please contact the Entrust Certificate Services Support department for further assistance:
Hours of Operation:
Sunday 8:00 PM ET to Friday 8:00 PM ET
North America (toll free): 1-866-267-9297
Outside North America: 1-613-270-2680 (or see the list below)
NOTE: Smart Phone users may use the 1-800 numbers shown in the table below.
Otherwise, it is very important that international callers dial the UITF format exactly as indicated. Do not dial an extra "1" before the "800" or your call will not be accepted as an UITF toll free call.
| Country | Number |
| Australia |
0011 - 800-3687-7863
1-800-767-513 |
| Austria | 00 - 800-3687-7863 |
| Belgium | 00 - 800-3687-7863 |
| Denmark | 00 - 800-3687-7863 |
| Finland |
990 - 800-3687-7863 (Telecom Finland)
00 - 800-3687-7863 (Finnet) |
| France | 00 - 800-3687-7863 |
| Germany | 00 - 800-3687-7863 |
| Hong Kong |
001 - 800-3687-7863 (Voice)
002 - 800-3687-7863 (Fax) |
| Ireland | 00 - 800-3687-7863 |
| Israel | 014 - 800-3687-7863 |
| Italy | 00 - 800-3687-7863 |
| Japan |
001 - 800-3687-7863 (KDD)
004 - 800-3687-7863 (ITJ) 0061 - 800-3687-7863 (IDC) |
| Korea |
001 - 800-3687-7863 (Korea Telecom)
002 - 800-3687-7863 (Dacom) |
| Malaysia | 00 - 800-3687-7863 |
| Netherlands | 00 - 800-3687-7863 |
| New Zealand |
00 - 800-3687-7863
0800-4413101 |
| Norway | 00 - 800-3687-7863 |
| Singapore | 001 - 800-3687-7863 |
| Spain | 00 - 800-3687-7863 |
| Sweden |
00 - 800-3687-7863 (Telia)
00 - 800-3687-7863 (Tele2) |
| Switzerland | 00 - 800-3687-7863 |
| Taiwan | 00 - 800-3687-7863 |
| United Kingdom |
00 - 800-3687-7863
0800 121 6078 +44 (0) 118 953 3088 |
