HSMs are an integral part of an enterprise’s drive to protect their data, providing a scalable infrastructure layer to support the increasing number of applications that require the use of cryptography to deliver security. However, as enterprises continue to look for efficiencies by moving away from traditional data centers and as security teams become more centralized, expectations of delivering everything (even security) as a consumable service are becoming paramount. Administrators, users and developers want to be able to access what they need quickly and efficiently, in the flow of their regular processes, and security teams want to create effective boundaries of responsibility to ensure policy decisions align with the relevant groups.
With this in mind, more and more enterprises are looking to deliver HSMs as a service as reflected In last year’s Global Encryption Trends Study carried by the Ponemon Institute and sponsored by Entrust . The study found that 61% of organizations now have a centralized unit that is using HSMs to serve up crypto-as-a-service to applications teams across their business.
The main drivers for delivering crypto as a service using HSMs are to manage scale efficiently without impacting users and their applications and to create a strong separation of duties to ensure security policy decisions are an integral part of the service. This strategy also negates the need for application owners to fathom everything out by themselves.
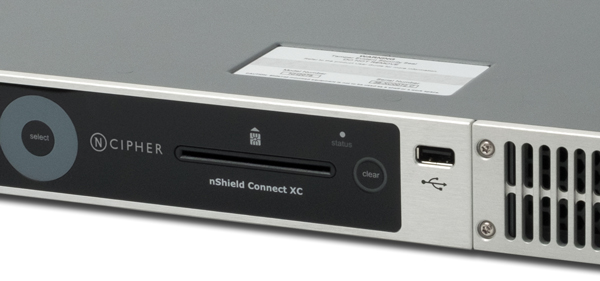
As the number and size of security applications increase, enterprises can make huge efficiency savings by pooling their HSM resources and allocating a share of the capacity to an application, groups of applications, internal departments or any other appropriate grouping based on their requirements. Further, using HSMs (such as nShield with Security World) designed to scale the resources allocated to an application or group of applications (without interrupting service to any applications using the HSM pool) will enable administrators to dynamically change the size of service and avoid overload situations or performance limitations.
Once enterprises have determined their strategy for grouping their users and applications, adopting appropriate key management policies will be equally important in maintaining the separation and isolation required between users of the services.
However, regardless of the policies enterprises choose, a significant advantage of creating a centralized service is that organizations can assign to their security teams the task of defining how those policies will be implemented. The policies might define user authentication requirements, the rights assigned to users and applications, the minimum strength of keys, allowed algorithms, and much more. The goal of putting policies in place is to ensure users will have no mechanisms to implement a different policy. The users are consumers of the service, and those responsible for the security properties of the service should set the policies.
With this method, enterprises can retain better control over their cryptographic assets and centrally manage security policies in order to more easily demonstrate compliance while delivering scalable security in an efficient and effective manner.
Visit our product page to learn more about Entrust’s HSMs. You can also follow Entrust on Twitter, LinkedIn, and Facebook.


