A strange question to be sure but indulge me. All ships leak. It doesn’t matter if it’s brand new or hundreds of years old. They all leak. How do they not sink, you might ask? Acknowledging that all ships leak, the builders have incorporated bilge pumps into their designs. A bilge pump removes the water that gets past the ship’s hull protection. Without bilge pumps, ships will eventually sink.
Now let’s extend this knowledge to a corporate network analogy. All networks can be penetrated. There. I’ve said it. There is no way to make a ship leak-proof and there is no way to make a network penetration proof. I know it’s a security architect’s job to try and create a more secure perimeter but there are limits to this effort. Try as you may, with the right hacking resources, time, money, and effort, every network can be breached.
If the hull of a ship is analogous to a network perimeter then what’s the analog for the bilge pump? Crypto. For the present and the foreseeable future, crypto is the silver-bullet against hackers. If properly implemented modern crypto cannot be broken. While there have been situations where a hacker has decrypted an encrypted database, in every case, however, the hacker has attacked the implementation of crypto and not the crypto itself. For instance, in 2018 when Marriott had their 500 million customer encrypted database stolen, the hackers decrypted the data and released the raw data to the world. This was not a failure of the crypto; it was a failure of encryption key protection. Basically, they stored the key with the data. This is like locking your door and leaving the key in the lock.
For someone who represents a company that sells cryptographic solution, referring to crypto as analogous to a bilge pump isn’t very glamorous. Luckily for me, glamor is never a requirement for something that’s critically important. No matter how much money a ship builder puts into making their hulls leak-proof, they’ll always employ a bilge pump. The secret is to determine how leak “resistant” a ship must be so that the bilge pumps can perform their final and most important job of keeping the ship afloat. Using this same analogy, companies need to determine their appropriate hacker resistant posture and let their crypto do the rest of the protection.
Recently I was talking with the CISO of a very large corporation. I asked him how much money he spent on his perimeter security every year. He reluctantly admitted that he spent over five million dollars annually. In comparison, he spent $500K on crypto solutions. As with almost everything in life, there this nasty thing called “The law of diminishing returns”. In corporate data protection, the money spent on perimeter security is far beyond the security afforded in return. This graph effectively represents this issue.
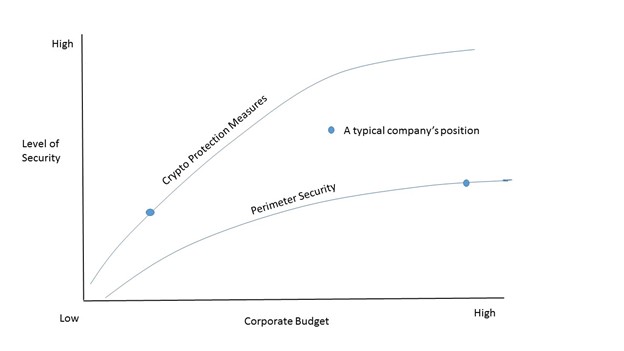
Somewhere on this Perimeter Security curve there must be a point where the perimeter is “secure enough” and companies must accept that a breach is inevitable. With the appropriately applied cryptographic protections , a company’s data assets won’t be compromised.
It’s understandable that many companies try to use perimeter security measure to attempt to protect their assets. A network engineer’s focus remains to protect their network first and the data within in second, and the unfortunate truth is that crypto is hard to understand and implement but it’s all we have that’s truly affective against hackers.
If after reading this article, I’ve convinced you that you’re better off investing in strong crypto solutions, I caution you to hire someone who really understands crypto and can apply it correctly. If you don’t implement crypto correctly, you might as well not do it at all.
All corporations today have some cryptographic elements in their systems already. Most have been implemented without an overall crypto plan. Most don’t know how many crypto applications they have and most don’t have full control over them. On top of that, more and more crypto solutions are being implemented in corporations, many without central IT knowledge or control. In today’s environments, crypto is unfortunately becoming the new “Shadow IT” issue.
There are four steps you can take as it relates to your crypto assets:
- Discovery – Find out what certificates and keys (crypto assets) are currently in use.
- Control – Once the certificates and keys are discovered, get them under some central control.
- Protection – All software generated and stored certificates/keys are vulnerable and can be found by hackers . Keys and certificates need to be moved out of software and into a hardware security module (HSM) and then rotate them as soon as possible to hardware generated and protected certs/keys.
- Management –This is an important step only because new crypto solutions are definitely in your company’s future and unless you start managing them now, it will be next to impossible in the very near future.
Learn the lesson from ship builders who realized long ago that the perfection of a ship’s hull isn’t possible and alternate measures must be employed to make sure that their ships don’t sink. These alternate measures are available today. Appropriately and effectively applied cryptographic measures will make sure your ship doesn’t sink when your network leaks.



