Recently the National Security Agency (NSA) provided an update on its security posture with regards to post-quantum computing. Hopefully you have not reached a saturation point reading about post-quantum cryptography because it’s a hot topic for science and the data security industry, with billions of dollars going into research in this space. It has huge implications for the entire IT industry and pretty much everything we do in our connected world. It’s encouraging to see the NSA has published this advisory detailing how they see things panning out, and in this blog I’m going to outline what it all means.
The NSA announcement comprises two documents; both are short and readable – thankfully no weighty 600-page tome to thumb through! Firstly there is the main paper, Announcing the Commercial National Security Algorithm Suite 2.0, and this is accompanied by a Frequently Asked Questions (FAQ) document, The Commercial National Security Algorithm Suite 2.0 and Quantum Computing FAQ. The FAQ provides a useful introduction to the post-quantum cryptography (PQC) topic followed by a set of Qs and As pertinent to the announcement paper. In terms of what algorithms are detailed in Algorithm Suite 2.0, readers following the NIST PQ competition and algorithm selection process will recognize CRYSTALS-Kyber and CRYSTALS-Dilithium, which are asymmetric algorithms for key establishment and digital signatures, respectively. AES is also listed as a symmetric block cipher for information protection. You should be familiar with that algorithm. I blogged about AES last year in celebration of its 20th anniversary. Recall that classical symmetric algorithms are considered in better shape for a post-quantum world than their asymmetric relatives. The Leighton-Micali Signature (LMS) is in Suite 2.0 too. This is a stateful hash-based signature that only uses hashes that are considered resilient to attack from a cryptographically relevant quantum computer (CRQC). It is a one-time signature scheme, meaning the private key must change for each signature. LMS has innate quantum-resistant properties as well as offering competitive signature sizes and reasonable signing and verifying times. LMS is already standardized in NIST SP 800-208 and the advisory goes on to state “NSA encourages vendors to begin adopting NIST SP 800-208 signatures immediately.”
Perhaps most interesting in the two documents is the timeframe. The FAQ document states the “NSA intends that all NSS [National Security Systems] will be quantum-resistant by 2035.”
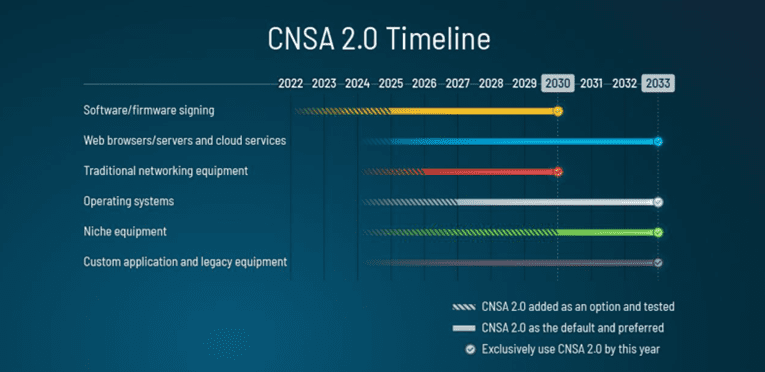
Figure 2: Transition timeline (source: NSA Cybersecurity Advisory, Announcing the Commercial National Security Algorithm Suite 2.0)
2035 feels like a long way off; however, Figure 1 from the announcement details a number of scenarios where more immediate timelines are in play:
- Software- and firmware-signing: Begin transitioning immediately, support and prefer CNSA 2.0 by 2025, and exclusively use CNSA 2.0 by 2030.
- Web browsers/servers and cloud services: Support and prefer CNSA 2.0 by 2025, and exclusively use CNSA 2.0 by 2033.
- Traditional networking equipment (e.g., virtual private networks, routers): Support and prefer CNSA 2.0 by 2026, and exclusively use CNSA 2.0 by 2030.
- Operating systems: Support and prefer CNSA 2.0 by 2027, and exclusively use CNSA 2.0 by 2033.
This is a clear line in the sand for organizations, suppliers, et al. involved with the U.S. national security agency. We are talking operating systems, web browsers, cloud servers, and software and firmware signing. That is quite a substantial list and represents a fair chunk of an organization’s IT ecosystem.
So what is the takeaway? Well, you’ll have heard it before but here it is stated clearly again by the NSA: “Now is the time to plan, prepare, and budget for an effective transition to quantum-resistant (QR) algorithms, to assure continued protection of National Security Systems (NSS) and related assets.”
For more resources on post-quantum click here. The Entrust Engage Series 1 podcasts on PQ can be found here.